1] B. Genge, C. Siaterlis, and M. Hohenadel. AMICI: an assessment platform for multi-domain security experimentation on critica
1] A. Avizienis, J.-C. Laprie, B. Randell, and C. Landwehr. Basic concepts and taxonomy of dependable and secure computing. IEE

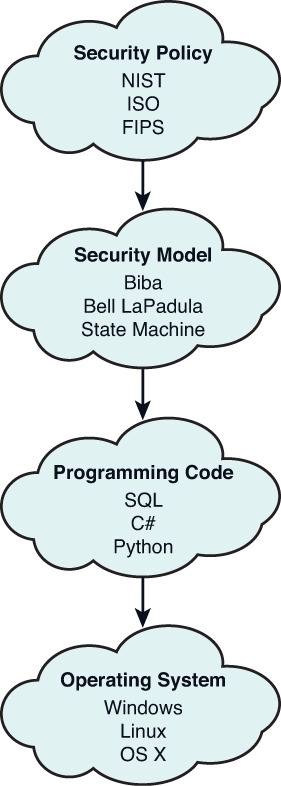
Comprehensive information security policy process model (Knapp et al.,... | Download Scientific Diagram



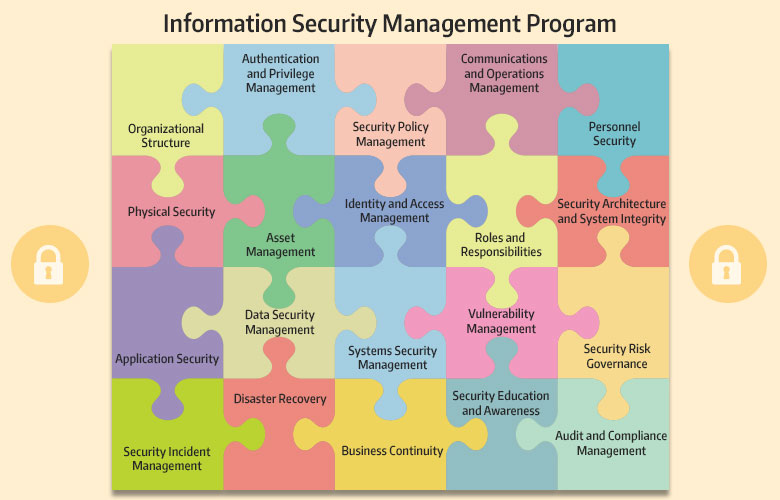





![PDF] Analyzing Information Security Model for Small-Medium Sized Businesses | Semantic Scholar PDF] Analyzing Information Security Model for Small-Medium Sized Businesses | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c8f1f0626a50a64962de125847fb373c91749c98/6-Figure1-1.png)
